If you want to run Tableau Server in a cloud hosted environment, like AWS, you may have concerns about unencrypted traffic between the nodes of the Tableau Server. Of course, you will have configured the Tableau Server to use SSL for external communications, and configured the internal repository to communicate via SSL, but what about data server, the data engine, etc.?
The best method to protect all of that communication is to enable IPsec via the Windows Firewall with Advanced Security pane in the Administrative Tools of Windows Server. I’m no expert on these things, so any questions, comments or discoveries are very welcome, but this seems to work in a basic AWS test cluster. I’ve heard you can control all of this policy stuff from a domain controller rather than configuring each machine, so don’t take this as the only way to configure IPsec.
You’ll do this process for each of the nodes that you want communication secured between. Once SSL is on for external communications, anything that would have passed over port 80 via HTTP should be passing over 443 using HTTPS, so I’m not sure whether a Gateway-only node would need the addition of IPsec.
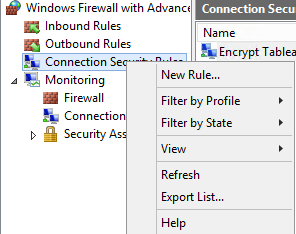
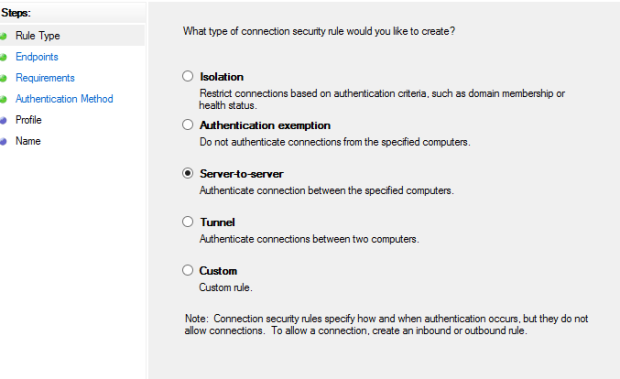
We want to make a single Connection Security Rule that will enforce authentication and encryption for everything on our nodes. Right click on the Connection Security Rule item and chose “New Rule…”
We’re just concerned with our intra-node communication right now, so make the rule a “Server-to-server” rule
Now we need to declare our endpoints. The first endpoint will be the server we are currently on
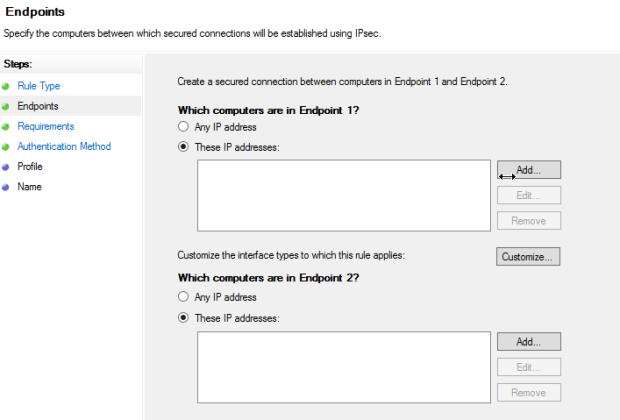
The Endpoint 2 IP addresses are all of the other nodes that this node might communicate with in the cluster. After this, on the Requirements page, chose “Require authentication for inbound and outbound connections”
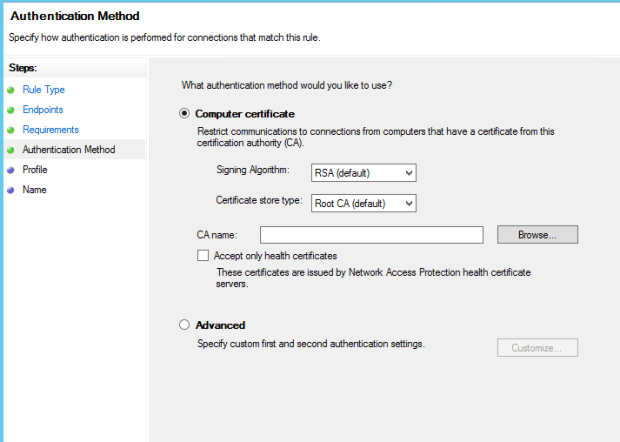
For your authentication method, you can use a certificate, or go into advanced and have your domain controller do the certification.
Choose your profiles (I selected for all) and give this rule a name, then press OK.
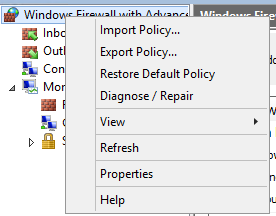
Now we need to configure the default for IPsec in the firewall so that it will encrypt all of the data using the method we prefer. Right-click on “Windows Firewall with Advanced Security” and choose “Properties”
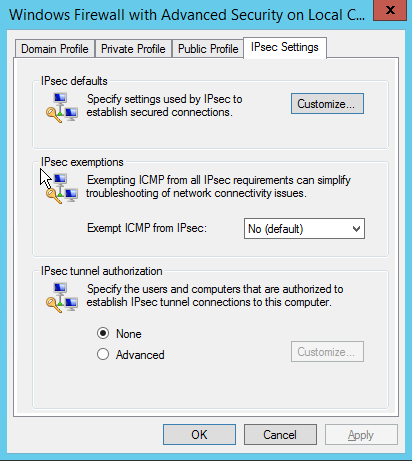
Go to IPsec Settings and choose “Customize” under “IPsec defaults”
When customizing the defaults, choose advanced for “Key exchange” and “Data Protection”, then Customize each of them
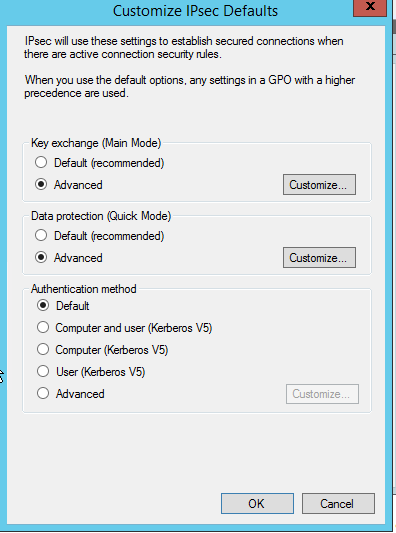
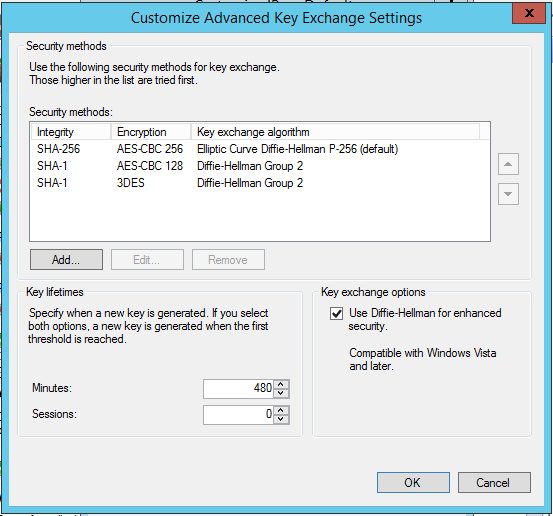
In “Key Exchange”, you should use some of the newer and more advanced settings, like SHA-256 | AES-CBC 256, and choose “Use Diffie-Hellman for enhanced Security”
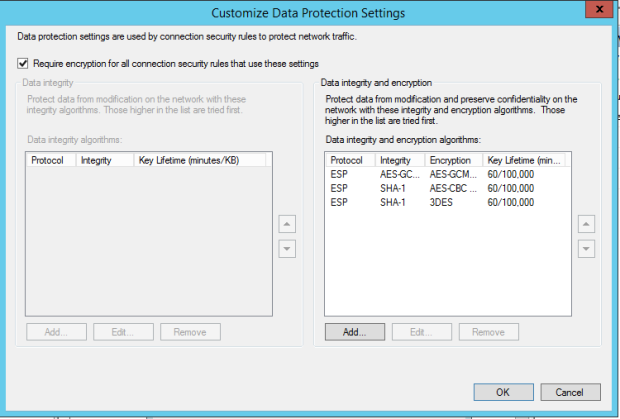
Under “Data Protection”, the essential thing is checking “Require encryption for all connection security rules that use these settings”. You should also add a better encryption algorithm at the top (I think I chose AES-CBC 256″ just like in my “Key Exchange”
Now press OK a few times, and turn on the Windows Firewall. Communication between the two servers will now be encrypted via IPsec (everything will go through ESP, Encapsulated Security Packets).
One comment